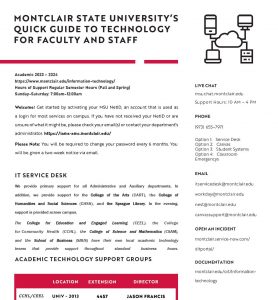
IT Services – Quick Links
New to Montclair?
News and Events
- IT Security Tips - Protect yourself from smishingThursday April 18, 2024

- IT NewsletterMonday March 18, 2024
- IT Security Tips: Federal Tax Time and IRS Related ScamsTuesday March 12, 2024

- DUO Universal PromptTuesday February 20, 2024
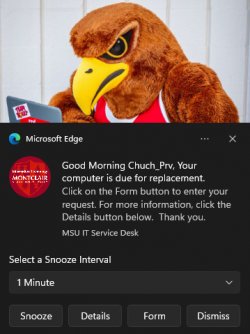
- New Lifecycle Replacement NotificationsFriday February 16, 2024
- IT Security Tips: Is It Me? (Protecting Yourself Against MFA Attacks)Tuesday February 13, 2024

System Status
Loading ...
Computer Lab Availability
Loading ...
About Us
The Information Technology Division is responsible for building, maintaining and supporting the University’s computing infrastructure. We support a wide range of technologies, encompassing enterprise servers and software, the University’s wireless and wired networks, campus phone networks, and desktop computers.
We also provide direct support to end-users – both employees and students – and run an assortment of computing and printing labs on campus.
Our goal is to make available the technical resources our students, faculty, and staff need to build a connected and effective learning environment for the information age.
Getting Help
The IT Service Desk link is ready to assist you if you’re having trouble connecting to the network, accessing any of the University’s online services, or obtaining needed software for your leased workstation.
- Phone
- 973-655-7971
- ITservicedesk@montclair.edu